Empower IT With Complete Visibility And Control
Automate data management to mitigate risk. Identity-Driven and Target-Driven policies in Senergy ensure that you’re always managing data assets properly. Senergy's policies handle data privacy, rights and access analysis, data disposition, and protection of high-value targets.
Save time and streamline security
With Senergy, You Can Create:
Identity-driven policies
Based on user identity and role, conducts lifecycle data management tasks including provisioning storage, assigning permissions, setting disk quota, performing data cleanup, and more.
Target-driven policies
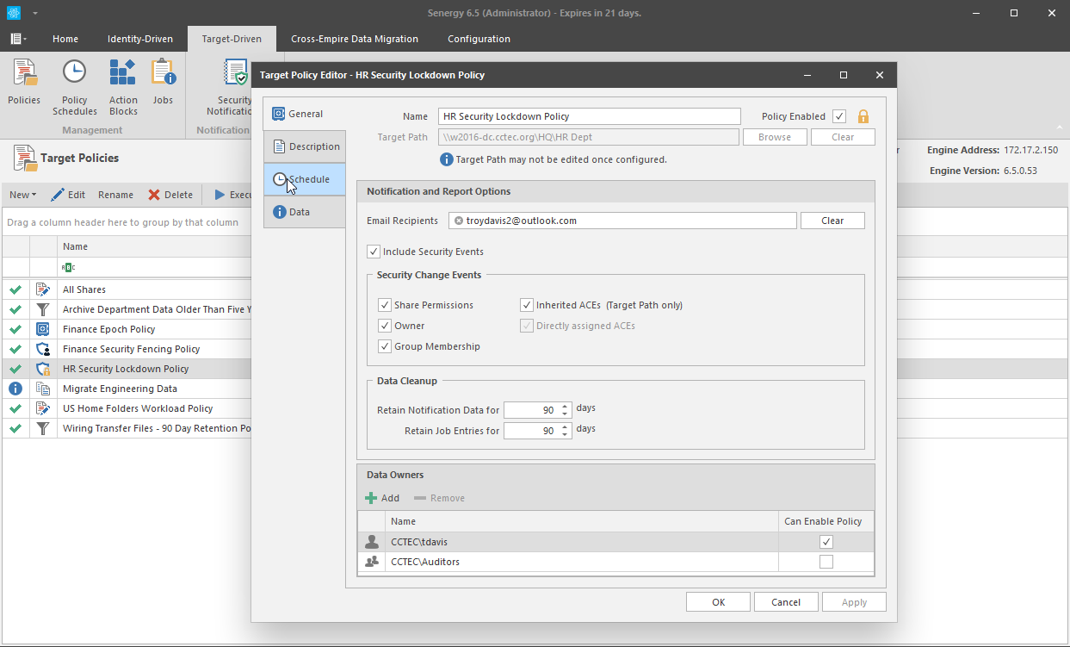
Through direct assignments to high-value targets, secures and protects data from unauthorized access, changes in access permissions, lost or corrupted data, and more.
Data Owner Task Management
Allows individuals familiar with the data to be notified of access permission changes, perform data recovery, or perform remediation of data located on high-value targets.
Keep Sensitive Data Secure
A series of security-based Target-Driven policies let you protect high-value targets from unauthorized access. Notification policies notify you when access permissions have been updated. Fencing policies restrict access to certain users and groups, and Lockdown policies prevent new users from being granted access.
Automated IT Data Management
Establish policies that automate IT tasks, including Data Access Governance. Migrate and load balance data across servers. Clean up and archive data in Windows shares according to file type, when files were last accessed, file size, and more.
User Home Folder Administration
Provision Windows home folders with access permissions and file structure according to policy. Automatically remove unallowable file types such as personal files. Clean up, archive, and delete home folders when a user leaves the organization.
Remediate the Location of Sensitive or Confidential Files
Address compliance requirements for securing confidential and sensitive files by providing Data Owners the ability to remediate the location of these files. When Galileo is combined with Senergy, Data Owners have the means of importing reports and then remediating problems. Data Owners can either move the files to a more secure location, delete the files, or change the ownership of the folder where the files are stored.
Manage Data Lifecycle
Through Identity-Driven policies that you define, automatically provision user and collaborative storage for all users in your organization based on their roles. These policies perform on-going management and can even automatically clean up storage when a user leaves the organization.
How do you secure your most important data?
Learn how Senergy does it!
Customer Stories
Organizations across the globe trust Condrey to protect their most critical data from exposure and attacks.
Migrating student home folders from one set of servers to another is normally an arduous event. But for one U.S. university’s IT department, it turned out to be easier than they could imagine. The university had been using Senergy from Condrey Corporation for years to automatically provision student home…
Read MoreProvisioning and managing network home and collaborative storage folders for this U.S. school district of more than 10,000 students and faculty used to be a process that took weeks to accomplish. There were the student and faculty user objects to create in Microsoft Active Directory (AD), the access permissions to set according to…
Read MoreThe Challenge Like most regulated industries, banks are required to protect the privacy of consumers’ finances under a federal law called the Financial Modernization Act of 1999 (also known as the Gramm-Leach-Bliley Act). The law governs how financial institutions can collect and disclose customers’ personal financial information, maintain safeguards to…
Read More