Gain Insight and Control of Your Data and Security in Microsoft Infrastructures
Achieve Management and Governance Goals through Analytics and Policy Driven Automation
Your Destination Defines Your Journey
The choice is yours; start a journey around data, identity, or remote access using the map. Then grow from there.
- Understanding the significance of data and its role in driving business success, we strive to help you navigate your path effectively.
- The destination you choose for your data determines the insights you can uncover, the decisions you can make, and the value you can create.
- Our expertise lies in assisting you in identifying the most suitable data destinations and architecting the infrastructure required to reach them.
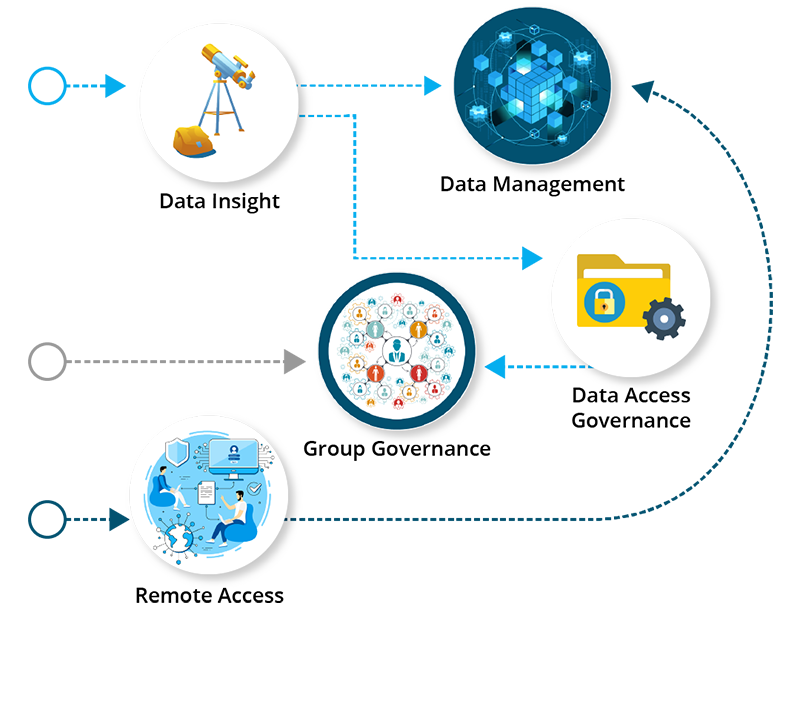
Understanding your data and the security of it.
ManagementAutomating the management of your data.
DAGSecuring Your Data with Data Access Governance
AccessAccessing and Sharing Your Data Where It Lives
GroupGoverning Groups in Your Enterprise
Achieve Better Data Governance through Our Identity-Driven software
Secure, role-based provisioning and meticulous automated control.
Visibility and Insight
Gain data and permissions insight through reports and graphical analytics tools to pinpoint actions you might need to address.

Automated Responsiveness
Establish policies that automate storage provisioning, data access, data cleanup, restoration of access permissions, and much more.

Security and Protection
Enforce and maintain compliance to regulations by keeping sensitive files secured from unauthorized access.
See It In Action
Data Management
Create automated policies for lifecycle management of user and group storage, archive or delete data that has expired, and move and structure data across the data center.
See It In Action
We Provide Data Solutions Differently
Condrey has been developing cutting-edge data technology for over 20 years.
We uncover every potential risk to your high-value data through thorough reporting and analytics, then help you automate control.
-
Delivery
Not only have we been building these solutions for 20 years, we’ve been delivering through our OEM network to the largest and most diverse organizations in the world.
-
Quality & Functionality
Our solutions can’t just work; our quest is for enterprise-class results with scalability and performance in the process.
-
Service & Support
Our mission from a Support perspective is to not just service our software, but work with you to help you get the results your organization needs.
-
Experience
Our team has always been built based on real world experience in IT management and consulting in large and demanding environments. This experience pays off in delivering effective solutions that address real world problems for you.
Industries We Serve
Our identity-driven software solutions are designed to cater to the unique needs of companies across diverse sectors. No matter the industry, we are committed to helping organizations optimize their data governance practices, enabling them to navigate the complexities of today's digital landscape with confidence.
Discover why organizations choose Condrey.
“Condrey Corporation has been listed as a representative vendor in every Gartner File Analysis market guide since 2014”
